Enhance Information Safety With Relied On Cloud Solutions
In today's interconnected electronic landscape, the relevance of improving information safety and security with relied on cloud solutions can not be overstated. By entrusting information to credible cloud carriers furnished with cutting-edge safety and security procedures, companies can fortify their defenses against cyber threats and make certain information discretion.
Significance of Data Security
Making certain durable data protection actions is paramount in today's electronic landscape to safeguard sensitive details from unauthorized access and cyber dangers. With the rapid growth of data generation and storage, organizations deal with increasing challenges in safeguarding their valuable properties. Information violations not just lead to monetary losses but likewise harm an organization's reputation and deteriorate customer count on.
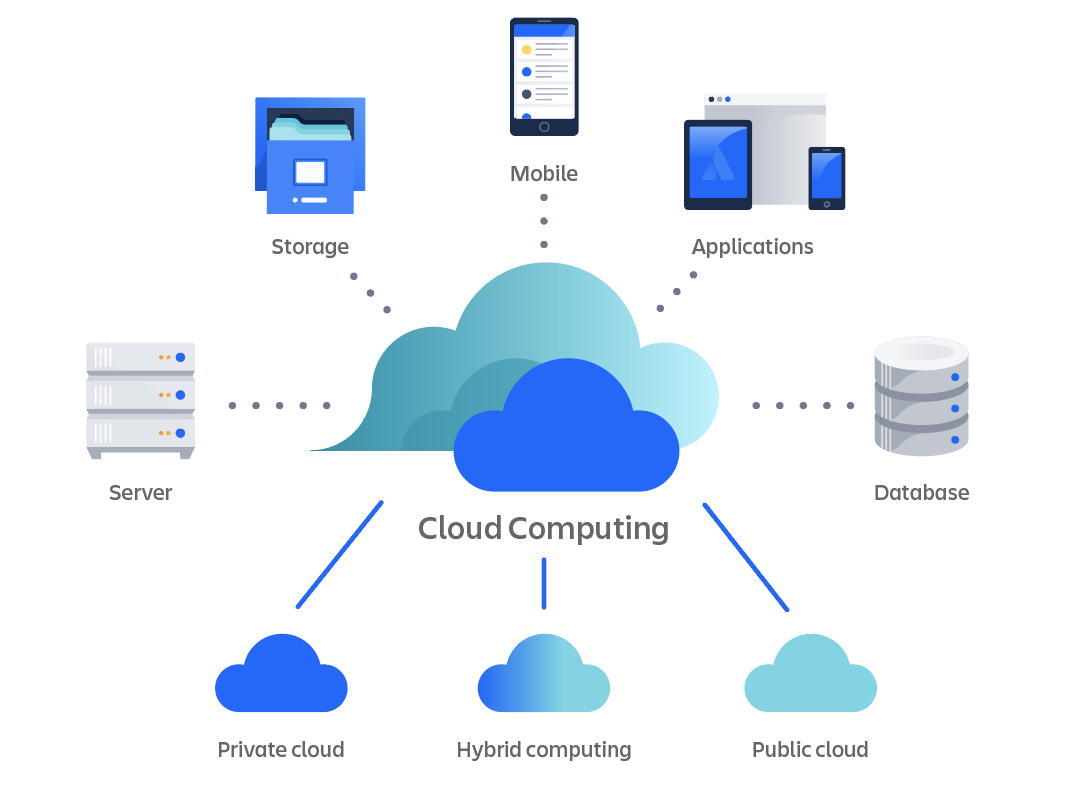
In the current period of remote work and cloud computer, the value of information safety and security is further amplified. Cloud solutions use flexibility, cost-efficiency, and scalability, however without ample security actions, they can present significant risks. As a result, companies must prioritize information security when embracing cloud solutions to avoid data breaches and support the stability of their operations.
Advantages of Relied On Cloud Providers
Given the climbing relevance of information security in the digital landscape, comprehending the advantages of trusted cloud services comes to be necessary for organizations aiming to fortify their data security techniques. Trusted cloud services offer numerous benefits that can improve information protection steps.

In addition, relied on cloud solutions provide reputable backup and calamity healing solutions, guaranteeing data accessibility even in the occasion of unanticipated occurrences. This reliability is essential for maintaining organization connection and decreasing data loss. Generally, the advantages of trusted cloud solutions contribute significantly to enhancing data safety methods within organizations.
Secret Features of Secure Cloud Solutions
Executing durable safety and security measures is necessary in ensuring the integrity of data kept and sent with cloud remedies. Additionally, protected cloud services supply multi-factor verification, calling for individuals to give multiple forms of verification before accessing the information. These attributes jointly add to an extra protected cloud look at this website setting, instilling self-confidence in customers click here to read pertaining to the protection of their data.
Best Practices for Data Protection
To fortify data safety in cloud settings, adhering to best techniques for information defense is paramount. File encryption plays a vital duty in safeguarding delicate details stored in the cloud. Implementing file encryption devices, both at remainder and en route, ensures that information is unintelligible to unapproved individuals even if it is obstructed. Accessibility control is one more vital method for information security. By enforcing rigorous access controls, companies can limit that can watch, modify, or delete information, lowering the threat of unapproved gain access to. Frequently backing up information is likewise a basic aspect of information security. In case of information loss or a protection breach, having up-to-date back-ups enables swift recuperation without jeopardizing valuable info. Furthermore, surveillance and auditing information gain access to and use assistance in spotting any kind of suspicious activities quickly. By adhering to these finest techniques for information protection, companies can improve their information safety position in the cloud atmosphere.
Choosing a Dependable Cloud Provider
Picking a trustworthy cloud supplier is an important decision for organizations seeking to enhance their information safety and security procedures. A trustworthy cloud supplier ought to have robust safety methods in location to safeguard data against unauthorized accessibility and cyber risks.
Furthermore, organizations need to examine the supplier's uptime and dependability performance history. Downtime can have substantial ramifications for business procedures and data ease of access, so choosing a service provider with a tried and tested record of high uptime is important. Companies ought to take into consideration the scalability and flexibility offered by the cloud provider to fit future development and altering organization needs.
Last but not least, assessing the provider's client assistance services is crucial. In visite site the event of any kind of issues or safety and security breaches, well-informed and responsive consumer assistance can make a considerable distinction in mitigating threats and making sure prompt resolutions. By thoroughly taking into consideration these aspects, companies can pick a trustworthy cloud company that satisfies their information protection requires effectively.
Verdict
In verdict, leveraging relied on cloud services is critical for enhancing data protection in today's electronic landscape. By applying robust encryption protocols, progressed threat discovery capabilities, and dependable backup services, organizations can successfully guard important details and mitigate dangers of information violations. Picking a trustworthy cloud provider and following ideal practices for data protection are necessary action in preserving data honesty and making sure extensive security versus cyber hazards.
By handing over data to trustworthy cloud providers furnished with sophisticated protection steps, businesses can fortify their defenses versus cyber hazards and make certain information privacy. Companies must focus on information security when adopting cloud services to avoid information violations and support the honesty of their operations.
Provided the climbing importance of information security in the electronic landscape, comprehending the benefits of relied on cloud services comes to be imperative for companies aiming to fortify their data security techniques.To fortify information security in cloud atmospheres, adhering to ideal methods for data security is extremely important. By complying with these best methods for data defense, companies can improve their information security pose in the cloud environment.